How to Protect Your OpenAI API Key in Frontend Apps (Without a Backend)
If your OpenAI API key is embedded in frontend JavaScript, it can be extracted and abused in seconds. The correct approach keeps your key server-side and lets your frontend call a secure endpoint instead.
- No Backend Required
- Server-Side Header Injection
- CORS Enforcement
- IP Rate Limiting
- Abuse Protection
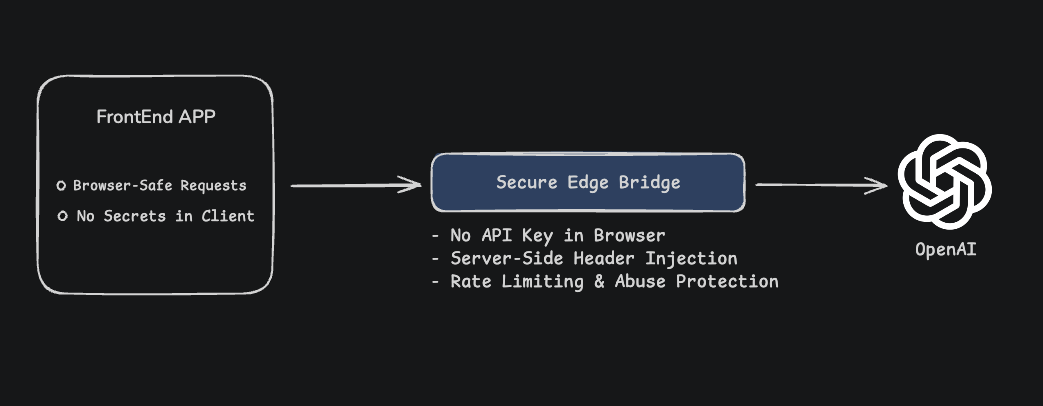
Secure OpenAI API Key Architecture
Why OpenAI API Keys Get Exposed
- Frontend JavaScript bundles can be inspected by anyone.
- Network requests reveal headers in DevTools.
- Bots automatically scan GitHub and public sites for API keys.
- Leaked keys can generate unexpected charges instantly.
Secure OpenAI Calls with a Server-Side Bridge
Instead of calling OpenAI directly from the browser, your frontend calls a secure edge endpoint.
The bridge injects your OpenAI API key server-side before forwarding the request.
CORS rules and rate limits protect your endpoint from abuse and misuse.
Related Secure Integrations
Secure OpenAI Request Example
javascript
const response = await fetch('https://api.salting.io/r/BRIDGE_UUID', {
method: 'POST',
headers: { 'Content-Type': 'application/json' },
body: JSON.stringify({
model: 'gpt-4o-mini',
messages: [{ role: 'user', content: 'Hello' }]
})
});
const data = await response.json();Frequently Asked Questions
Protect Your OpenAI API Key Today
Stop exposing your OpenAI key in frontend apps.
Create Secure Endpoint